SHA1:
- SHA1: 82e0fd8db296aeb88237fe80711d25dd63fdca80
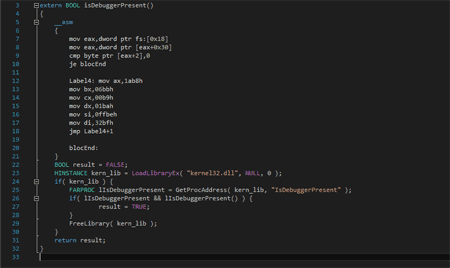
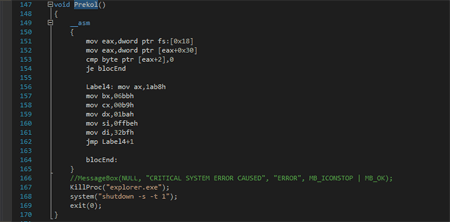
The following development of the miner Trojan.BtcMine.1959. Its self-designation is Gefest. Once launched, the Trojan implements anti-debugging features:
In case of detection of a debugger, the miner shuts down Windows Explorer and restarts the computer:
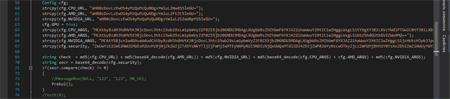
Then the Trojan checks whether its configuration has been changed without authorization via checking MD5 hash:
Check of relaunch is performed using mutexes. Then the Trojan checks whether it operates independently or it is embedded into a system process: this check is performed by determining a path to the process executable file and an attempt to find in this path a substring “windows” or “WINDOWS”.
If the Trojan is launched as an independent application, it saves its copy into the file “%PROGRAMDATA%\\<hwid>\\<hwid2>.exe”, where hwid is a string obtained from the registry key [HKLM\\SOFTWARE\\Microsoft\\Cryptography] 'MachineGuid', and hwid2 is first five symbols of MD5 from hwid. Then the miner generates a list of all files with the EXE extension located in the folder %SYSTEM32% by randomly sorting them. It also tries running each file from the list with the flag CREATE_SUSPENDED and embedding it into file’s memory—up to the first successful attempt.
If the Trojan is embedded into a running process, it tries to determine whether a computer is equipped either with the Nvidia or AMD video adapter. If such adapter is found and the Trojan’s configuration has a flag installed that allows using GPU for cryptocurrency mining, the Trojan extracts from the configuration a link to the miner and its launch parameters. After that it downloads and embeds the miner into an arbitrary process according to a scheme described earlier. Regardless of the miner’s usage for graphics adapters, the miner for CPU is always downloaded and embedded into other processes.
Sometimes the Trojan checks the presence of its file on the disk and saves it once again in case of its removal. Using the name detection of open windows, the Trojan tracks launch of various applications that allow tracking running processes:
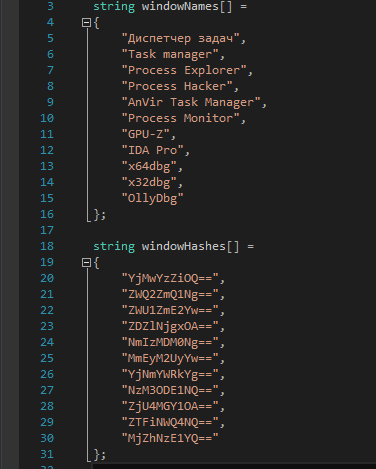
When detecting a program from the list, it shuts down the process with the embedded miner and relaunches it when the respective application is unloaded.