sha1:
- 673b6be8163580ba70403321663f5edbb0565f12
- feb0501ac141df63cc0d5bb341cb24a769f81bc9
- bfab9c8da1f969b07e4e7f0bd1aa9865fd7a9d3c
- 5918bbf71641c2776f20bdd2fc08c82dc17178cc
Description
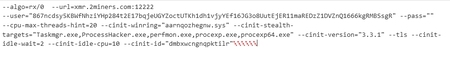
A trojan miner for Windows OS written in C++. Depending on the type of coins being mined, it can be based on the code of either XMRig or ETHmine. The miner is injected into explorer.exe by its loader Trojan.BtcMine.3767 via the SetContextThread function. When the process is created, its Shellinfo variable in the RTL_USER_PROCESS_PARAMETERS structure accepts a string containing the miner configuration, encrypted with AES CBC, and additionally encoded with base64. The key is UXUUXUUXUUCommandULineUUXUUXUUXU, and the initialization vector is UUCommandULineUU. After decryption, the miner configuration looks like this:
In addition to the settings inherited from XMRig, Trojan.BtcMine.2742 accepts the settings provided by its loader, compiled using the SilentCryptoMiner project.
| --cinit-winring= | Contains a path to the previously created winring file |
| --cinit-remote-config= | Contains a link to download miner settings every 100 seconds |
| --cinit-stealth-targets= | Lists the applications that, when launched, will cause the miner to free up video memory and RAM |
| --cinit-stealth-fullscreen | This flag tells the miner to pause mining when an application is running in full screen mode. The SHQueryUserNotificationState function performs the verification |
| --cinit-kill-targets= | Kills the specified processes when they are detected |
| --cinit-api= | Contains the URL of a web panel used to monitor and control the miner |
| --cinit-version= | Contains the SilentCryptoMiner version |
| --cinit-idle-wait= | ПIf no user activity is detected within the specified time, the miner's maximum CPU utilization will change |
| --cinit-idle-cpu= | Maximum CPU utilization by the miner if no user activity is detected |
| --cinit-idle-gpu= | Maximum GPU utilization by the miner if no user activity is detected |
| --cinit-max-gpu= | Maximum GPU utilization when IDLE mode is turned off |
| --cinit-id= | Contains the name of the created mutex |
| --cinit-algo= | Sets the mining algorithm |
Indicators of compromise:
- 673b6be8163580ba70403321663f5edbb0565f12
- feb0501ac141df63cc0d5bb341cb24a769f81bc9
- bfab9c8da1f969b07e4e7f0bd1aa9865fd7a9d3c
- 5918bbf71641c2776f20bdd2fc08c82dc17178cc