The Trojan for Android devices. Android.MulDrop.46.origin is a dropper designed to distribute other malicious programs, for example, Android.BankBot.35.origin, among Android mobile devices. The backdoor can be distributed by cybercriminals under the guise of a popular browser or some other legitimate software.
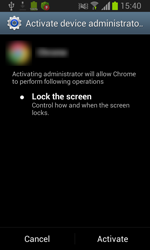
Once it is installed on the mobile device, Android.MulDrop.46.origin can be launched using different methods. For example, the user themselves can launch the Trojan by tapping the malware’s shortcut on the Home Screen. In that case, Android.MulDrop.46.origin prompts the user to grant it administrative privileges and deletes the shortcut. Moreover, the Trojan can launch automatically when the operating system is loaded or when the device’s screen is unlocked (by using control of android.intent.action.BOOT_COMPLETED and android.intent.action.USER_PRESENT system events respectively). Once it is launched, Android.MulDrop.46.origin operates as a system service.
Malicious activity
Using the DexClassLoader class, Android.MulDrop.46.origin loads an executable DEX file stored inside of the backdoor’s program package into the infected device’s RAM. This file is a Trojan (can be detected as Android.BankBot.35.origin) designed to install other malicious applications on the system (for example, a banking Trojan Android.Banker.46.origin) and to execute various commands issued by cybercriminals.
The Trojan’s malicious functionality can be also used by Android.BankBot.35.origin to run downloaded DEX files.