SHA-1:
- e4627cb007e850951d517a9df6e2d85fd47bf380 (crx)
- 6cd9411ba0bf32e652b6c4d0d196354b48d67164 (back.js)
- 4741b9e5de51828087b04fa466338248eb490d17 (page.js)
Trojan made as a Google Chrome browser extension. It is designed to perform web injections into webpages viewed by users and to block third-party advertisements.
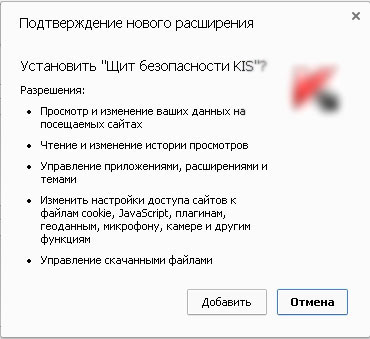
An incident of Trojan distribution using automatically opened tab in a browser window was detected. This tab does not allow to close itself and shows a window offering to install this malicious extension. Trojan is distributed under the name “Щит безопасности KIS” (KIS Security Guard) and consists of two obfuscated files written in JavaScript: back.js and page.js. The plug-in has the following manifest:
{
"update_url": "https://clients2.google.com/service/update2/crx",
"background": {
"scripts": ["back.js"]
},
"content_scripts": [ {
"js": ["page.js"],
"matches": ["*://*/*"],
"run_at" : "document_start"
} ],
"icons": {
"128": "icons/128.png"
},
"name": "Щит безопасности KIS",
"description": "Защита вашего пк от вредоносных ссылок и программ",
"manifest_version": 2,
"content_security_policy": "script-src 'self' 'unsafe-eval' https://ssl.google-analytics.com; object-src 'self'",
"version": "2.5",
"permissions": [
"storage", "tabs", "webRequest", "webRequestBlocking", "unlimitedStorage",
"webNavigation", "<all_urls>", "notifications", "cookies", "downloads", "history",
"management", "contextMenus", "contentSettings", "http://*/*", "https://*/*", "topSites"
]
}During installation, the plug-in requires the following privileges:
A core set of Trojan functions:
- injecting random JavaScript script received from the command and control server into the webpages;
- blocking showing third-party advertisements at all websites, except those that are listed in the configuration;
- disabling Chrome extensions upon receiving a command from the server;
- misusing the user’s account in the “Odnoklassniki” social network;
A list of “trusted advertisers” contains the following domains:
['onclickads.net', 'gettraff.com', 'tralfslab.ru', 'trafflabos.ru', 'trafficserving.com', 'mxttrf.com', 'cdn.staticwebdom.com', 'statsmobi.com', 'smaclick.com', 'openx.net', 'news.smi2.ru', 'pagead2.googlesyndication.com', 'content.adspynet.com', 'betweendigital.com', 'code.d-agency.net', 'js.smi2.ru', 'xwell.ru', 'admail.am', 'switch.d-agency.net', 'doubleverify.com', 'tpc.googlesyndication.com', 'redir.adap.tv', 'dtm.advertising.com', 'pagead2.googlesyndication.com']Trojan.BPLug.1041 sends user ID and data about other Chrome extensions installed at the infected computer to the cybercriminal server. During sending data, server may specify the Trojan which extensions should be disabled. Reply from the command and control server may have the following structure:
config<!><!><!>page_insert_script<!><!><!>page_run_script<!><!><!>page_onmessage_script<!><!><!>back_background_script<!><!><!>back_onmessage_script<!><!><!>back_handle_response_scriptSeparate function is responsible for showing advertisement. With the help of this function the Trojan analyzes the content of a webpage opened by a user. If its context includes sexual content, Trojan.BPLug.1041 loads advertisement of the corresponding subject from two separate networks. This extension also contains the list of websites where the Trojan does not show advertisement:
['govweb.ru', 'fsb.ru', 'gov.ru', 'government.ru', 'mos.ru', 'gosuslugi.ru', 'gks.ru', 'vk.com', 'google.ru', 'youtube.com', 'google.com.ua', 'ru.wikipedia.org', 'yandex.ru', 'google.by', 'google.com', 'market.yandex.ru', 'mail.google.com', 'images.yandex.ru', 'avito.ru', 'pikabu.ru', 'mail.ru', 'instagram.com', 'facebook.com', 'steamcommunity.com', '2ch.hk', 'yandex.ua', 'habrahabr.ru', 'ok.ru', 'odnoklassniki.ru', 'en.wikipedia.org/wiki/Main_Page', 'sberbank.ru', 'mvd.ru', 'ya.ru', 'mail.yandex.ru', 'mail.rambler.ru', 'rambler.ru', 'booking.com', 'marketgid.com', 'qiwi.com', 'qiwi.ru', 'kak-nauchitsia.ru', 'news.tut.by', 'superjob.ru', 'vihrov.blogstop.com']If a user makes a log in to the “Odnoklassniki” social network, Trojan.BPLug.1041 tries to provide a certain application with the access to the API of this social network under the user name by means of the authorization by OAuth protocol. During this process, privileges are required to change the status, view, edit, and upload photos; viewing and sending messages under the user name and some others.
There are three more extensions under the name “Щит безопасности KISi” (KIS Security Guard) in Chrome extension online store. All these extensions are created by one and the same author, but the functionality of two others reduces to loading scripts form the command and control server.
- f347dc275dcc6acee1f658bed64f8ea4908c0ac5 (crx) - extension_id dogojpdglbhldjonllhpghgalomnljgo
- 50d8466b72d06ae6086489ceefbe295e14f7b8ab (crx) - extension_id hglilpokbpmhgcgmlgkdchepkbdefkaj
- 95dafb355559fce5249d7cc419ba80565d719e23 (crx) - extension_id mebffcdicpfbajjjgiconipfgomhoido
